What is he talking about, public WiFi can easily poison and monitor your DNS requests (most people don’t know or use encrypted DNS), and there’s still tons of non-https traffic leaks all over the place that are plain text. Even if encrypted, there’s still deep packet inspection. VPNs can mitigate DPI techniques and shift the trust from an easily snoopable public WiFi to the VPN’s more trustworthy exit servers.
This guy really needs to elaborate on what he’s trying to say when the cyber security field very much disagrees with this stance. I’m not a huge fan of Proton, but they aren’t doing anything wrong here. You should use it for public Wi-Fi.
Yup. You can grab any unencrypted data passed between the user’s browser and a server literally out of thin air when they’re connected to an open access point. You sit happily at the Starbucks with your laptop, sniffing them WiFi packets and grabbing things off of them.
Oh and you have no idea what the myriad of apps you’re using are connecting to and whether that endpoint is encrypted. Do not underestimate the ability of firms to produce software at the absolute lowest cost with corners and walls missing.
If I was someone who was to make money off of scamming people, one thing I’d have tried to do is to rig portable sniffers at public locations with large foot traffic and open WiFi like train stations, airports, etc. Throw em around then filter for interesting stuff. Oh here’s some personal info. Oh there’s a session token for some app. Let me see what else I can get from that app for that person.
Just FYI https://shop.hak5.org/products/wifi-pineapple. There are ready-made devices that can do basically what you are describing!
Oh nice. Just gotta dress em up like Unifi or Aruba then stick em up on the ceiling.
Yep, my partner gave one for my birthday, it’s basically plug-and-play. It can automatically harvest credentials, spoof captive portals, etc. I bet that in most places nobody would question something like this hanging on the ceiling indeed.
We need a switch like Firefox has that disallows anything non-HTTPS, but from the phone level. Companies like Apple and Google could also eventually warn apps that they’re going to make it the default setting.
Apps don’t use the system browser to connect to REST endpoints. Neither do they use the OS. Apps typically use a statically linked library. There are use cases for HTTP-only connections so it’s unlikely that those libraries would mess with forcing or even warning its users that they’ve used HTTP instead of HTTPS. Point is Google and Apple can do little in this regard. Unless they scan apps’ source code which could be possible to some extent but still difficult because URLs are often written in pieces.
Sure, I didn’t say they use the system browser - I said the opposite. I’m saying the OS should be able to block non-HTTPS connections. If you have control of the OS you can control what protocols are used by apps, unless I’m missing something.
What cases are there for non-HTTPS? I can’t think of any. It’s 2024. All communication should be encrypted.
The OS interfaces provided to apps (generally POSIX) have no idea what HTTP is. They’re much lower level than that. If an OS is to control what protocols are used by apps, it has to offer some functionality that does HTTP for the apps and apps have to use it. Unfortunately the only way to force that would be to disable the general OS interfaces so that apps can’t just use existing libraries that use those. If you did that your OS would become useless in other ways that rely on the basic interfaces.
The other way the OS could do anything about it is to inspect network traffic going over its network interfaces. That would be a significantly different can of worms and it’s not free in terms of processing power and therefore battery. Then you’d have the screams of privacy people that Android or iOS is looking at all network traffic.
So all in all, the OS isn’t very well suited to police application level protocols like HTTP. At least not on devices whose primary purpose isn’t network traffic related.
Also, any unlatched, unfirewalled vulnerabilities you have are immediately available to anyone on that local WiFi network. One thing VPNs may do is cause you to ignore requests from systems on the local network, which helps.
That’s an interesting one. I know it depends on configuration, but in the run-of-the-mill case, does connecting through VPN stop local services to listen on local IPs? I know our corpo VPN kills local LAN access but I’m curious what the default for OpenVPN/Wireguard might be.
How is DPI a problem if it’s encrypted? That would only work if the attacker had installed their CA cert on your client machine, right?
I’m doing DPI on my own network and I can still view TLS certificate fingerprints and some metadata that provides a good educated guess as to what a traffic flow contains. It certainly better that it’s encrypted, but there is a little information that leaks in metadata. I think that’s what was meant.
True, but this is generally not useful information to anyone. They can see you’re visiting bank.com, but they still can’t see your bank details.
It might be useful if they’re trying to target you for phishing, but a targeted attack is extremely unlikely.
Also, any wireless equipment from the past 15 years or so supports client isolation.
Client isolation doesn’t help. That is just the access point not routing traffic between connected devices. The problem with WiFi is it is a radio signal. Everybody in range can receive 100% of all communication on that network. Just by being in range the attacker can do passive sniffing. No wiretap needed like with cabled networks.
WiFi is encryoed if it uses a password. So any public WiFi without a password can be sniffed by literally every device in range (no need to connect to the WiFi for sniffing). On public WiFi with a password, the radio signal is encrypted but everybody knows the encryption key. So everybody connected to the WiFi can still sniff the traffic of everybody else.
That encryption is only on the WiFi level, so encrypted radio signals, not on the actually traffic level (like TLS/HTTPS etc).
I think it might be confusion between inspecting plaintext metadata like SNI vs actually inspecting encrypted contents (e.g. HTTPS content, headers, etc.).
Yeah, deep packet inspection really doesn’t work without breaking https security via man in the middling everything.
Dpi only works if they install a cert on your phone. Else they can’t crack it (in real time) or you would receive HTTPS errors
You dont need to examine the contents of http traffic to do what many services call DPI.
you can still read unencrypted traffic, like most DNS. Or even without that, you can frequently tell from the endpoint IP who someone is talking to, and what types of applications from port numbers used. Etc.
If you’re torrenting, for example, that’s pretty easy to see.
Still not DPI. Regardless of what other manufacturers or devs call it.
At best it’s a network monitor. Literally pihole can give you most of those stats as well.
deleted by creator
Yeah, while it is true, lots of VPN companies are grifts just buying VPS’s and installing OpenVPN, this “Cyber security expert” puts far too much faith in HTTPS and probably never seen a lecture from the Black Hat conference
probably never seen a lecture from the Black Hat conference
Not defending Robert Graham because I’m also eyebrow raising his statement. And while you may be 100% correct that he never actually stayed to listen to a lecture, he absolutely spoke at a lot of them since 2000.
My bad for judging without checking 😔
Many VPNs using OpenVPN is…fine.
The value adding is the VPN infrastructure they’re providing. You can’t just install the standard OpenVPN client and expect it to DO anything without some kind of service.
True on the HTTPS thing.
I’m not even an expert in this stuff, but with a tool I found online I demonstrated that it was easy to snoop people’s passwords on my school’s wifi networks back in the day. It took minutes.
That must’ve been quite a while ago
I mean, yes, I’m in my 40s, but it’s just as effective today.
I’m sorry, but I don’t believe it is. Nearly all traffic is TLS. When this is attacked, you’d get TLS error. Am I missing something?
There exist plenty of services on school campuses that send passwords in plaintext. There are services outside of school campuses that do, too. Hell, I’ve been able to bypass 2FA checks by just navigating around them, I don’t know what else to tell you, not everything out there uses the best security practices, so don’t assume that they do.
I guarantee you it’s not.
most people don’t know or use encrypted DNS
But a cybersecurity expert does. That’s the point. If you know those things, VPNs become obsolete, for most people. So why not teach people about it, instead of promoting VPNs?
And can you really trust an extremely profit focused company, that is built on user data, more than your local Café? If you’re in China, sure, use a VPN, they’re the lesser evil. But most spots don’t have the resources or expertise to analyze and sell or otherwise misuse your logs. VPN companies not only do, most rely on it.
If you’re a highly targeted person, it’s another story, but in that case your only hope is Tor or a new identity.
Proton is a non profit.
But Proton Bad? I don’t understand. The armchair security nerds on Lemmy want me to hate something.
I agree here. It’s clear that some people here really want me to be outraged at SOMEONE, but dont seem to really understand who or why.
So why not teach people about it, instead of promoting VPNs?
Ok then, in the meantime the rest of us will use a fucking VPN? I don’t know what “encrypted DNS” means, and I’m 99% you’re going to respond with either “whaaaaat you don’t know something that 99.999% of other people also don’t know? Clearly you are too dumb for the internet” or else “oh sure I’d be glad to explain that! It’s real simple, see when you have a Rosendin gembal, it befrazzles the gesticulators of your brangles (link to a Wikipedia article on brangles). So you just have to re-delineate the scanditrons to break the tensor lines in your scintrins! You can code a fairly simple app from scratch to do it, and there’s a FOSS program someone made to help you identify the cabangs in your computer’s lenticles: (link to a github page that is literally just a transcription of an eldritch god screaming in binary)”
VPNs are extremely user friendly and they are happy to explain in layman’s terms exactly what they do and how they work. If there’s a better way, it’s locked behind years of techie knowledge.
And most users don’t know what a VPN is. In both cases, they’re not gonna learn anything about it. Except you need to pay for a VPN, after figuring out which one is kinda trustworthy instead of snakeoil, while encrypted DNS is a simple setting on any OS. Nothing more. You don’t need whole articles to explain what your product does and why you respect privacy and blah, while not saying a single word that’s true. It’s a simple setting. VPNs are not only user friendly, they’re a full ripoff for most people and snakeoil. They don’t explain what they do in “laymans terms”, most of them just blatantly lie. Anything for the cash. If you want an explanation of encrypted DNS:
A DNS is kind of like your GPS. It translates an address into something more usable, e.g… like your GPS translates ‘123 Baker Street, Washington’ into coordinates, so you can use it on a map, for example. A DNS does the same, but for the internet: It translates “google.de” into a format that is actually readable and usable to the computer. However, to translate “google.de” you need to reach out to someone else, that knows the address. The thing is, if someone just pretends to give the right answer, but in fact gives you their own address, you may end up at the wrong website, or in the GPS example, at the wrong house. So instead of visiting your actual bank’s website, you’re going to visit someone else’s website, which looks basically the same, except once you log into your bank account the attacker can read that and steal all your money. In the GPS example, you would now be at the slaughterhouse instead of Disneyland. An encrypted DNS just means that you specify exactly whom you will trust, for example google, and that you want your communication with google to be encrypted, so no one can even read which website you want to visit.
If someone doesn’t understand this, they wouldn’t understand what a VPN is, even broken down to bare concepts. So for those people: It makes you safe just trust me just set this setting, no app, no account, no money required. Because that’s the level a typical VPN company argues on.
It seems like your whole threat model is avoiding DNS poisoning, which is fine, but I fail to see how you can compare using DoH/DoT to a VPN.
so no one can even read which website you want to visit.
Except for the DNS provider (in your example, Google, so… yikes), the operator of the network you’re on (since the destination IP can be rDNS’d or WHOIS’d, or simply grabbed from the Host header if your browser still tries HTTP first). Any traffic that is not encrypted will be snoopable. Traffic volume and connection times to each destination can be analyzed.
By contrast, a VPN will also use secure (if you trust the provider ofc) DNS servers for your requests, plus making all of the traffic completely opaque except for “going to this server”.
no app, no account, no money required
You can also make your own, free VPN service with a little technical knowledge.
VPNs are 95% about privacy, not security. So all encrypted DNS does is security? What I want from a VPN is fewer companies accurately spying on me.
Encrypted DNS doesn’t solve everything. Handshake for TLS sessions is still in clear, you can usually see the SNI, and since we are talking about Wireless, usually this data is available to anybody who is in the vicinity, not just the network owner. This already means that you can see what sites someone is visiting, more or less. TLS 1.3 can mitigate some of this (for those who implement ESNI, but you don’t know that beforehand). Also TLS works until the user is not accepting invalid certificates prompts (HSTS doesn’t work for everything) and there are still tons of HTTP-based redirect (check mailing newsletters and see how many first send you to an HTTP site, for example) that can be used for MiTM attacks.
A VPN moves the trust to a single provider that you can choose, which is much better than trusting every single WiFi network you can attach to and the people connected to it, I would say.
Also if you pay for the VPN (I pay Proton), it’s not true that the company business is based on user data, they are based on subscriptions.
Lmao, we’re not worried about the cafe. We’re worried about the man in the middle. And yeah with enough tech knowledge you can set up an encrypted tunnel home and use your normal connection from there. But most people aren’t that tech savvy
If you’re not relatively tech savy, a typical VPN IS the man in the middle. That’s the problem. A VPN, in itself, is very good. But as you said, non-tech savy users won’t be able to set up a VPN themselves, so they need to trust a company to route all their traffic, be their DNS server, not log anything, not be hacked and not give any data to current or future totalitarian governments. Not even I could recommend any VPN company that fulfills enough points there, especially the security related ones.
For the average person, data sales aren’t the worry. Heck their phone is already recording everything. The worry is straight up criminal enterprise, like keylogging bank passwords. If the VPN company is doing stuff like that then they’re going to eat a RICO charge. Most people really don’t care that their data gets sold.
And then just setting a private DNS and checking “the little lock at your address bar” fully prevents any digital sniffing of your credentials. No VPN needed.
But most spots don’t have the resources or expertise to analyze and sell or otherwise misuse your logs.
Most spots don’t have also the resources or expertise to secure their own spot. As I remember, cheap routers used in public places may contain a lot of vulnerabilities.
encrypted DNS
Will it help me if I’m using LbreTorrent do download piracy content on my phone? Or how it would help me to hide my location from mobile apps that extract location from IP?
No. That’s a whole different use case. We’re discussing what most people in a public network should do. Some people, such as whistleblowers, journalists etc. maybe should use a VPN. For you grandparents, it would be pure snake oil. And even as such an endangered person, choosing the wrong, so almost all, VPNs would be even more dangerous.
For your problems, a VPN could be useful, even though for the former I would use the usenet or soap2day-like sites, which do not have you seed that content. If you still want to share it, then use a VPN. ONLY for the torrent process, not for anything else, as that would still be bad for privacy and security, as the VPN company could, and most WILL, surveil and log you. And for the latter problem, don’t use such apps except in closed environments or without internet access.
And for the latter problem, don’t use such apps except in closed environments or without internet access.
While that is a right answer, I do not want to avoid such apps because I need them. I need my mobile bank app, I need google camera, sometimes I need Google maps, etc. For me using VPN to hide my real IP from greedy apps and to hide DNS requests from the cracked public WiFi is still a good tradeoff between security, privacy and my own user experience.
If it works for you, and you found a VPN provider you can trust, or at least have the feeling of that, great! That is one of the very rare use cases where VPNs are not only useful, but actually have a purpose.
On a broader scale, most people won’t find a trustworthy VPN, and would use it for way more than they need to, essentially giving all data to the VPN company now, instead of just to the local Café or google.
And for the bank app, there is no replacement. Google’s camera can be replaced by OpenCamera, or just disallowed to access the internet, and google maps can almost perfectly be replaced by organic maps
I have Pixel with GrapheneOS and I tried most of FOSS camera apps, but all of them are still far behind the GCam. I hope one day there will be a good replacement, but not today.
I’m using Organic / OsmAnd for most of use cases and daily navigation. But if you need to find a specific office, shop, food or ATM nearby you still need GMap from time to time…
Doesn’t Graphene not support Gapps at all?
People can’t learn not to throw trash in the street, climate change that is backed by decades of science is a problem, or hell, they can’t even learn to effectively not click on super suspicious phishing links.
How on earth are they going to learn about implementing encrypted DNS when most barely know the difference between a browser and a computer.
99.9% of people don’t throw trash in the street.
At least in most countries.
Lol look at statistics of smokers. Waaay more than 0.01% of people in any given country and 90% of smokers throw cigarette butts on the ground. That is just that one example.
If you have ever traveled to the southern US, oof.
Then they won’t know what a VPN is either.
I’ve never really understood that argument. Most VPN software I’ve seen forces your DNS through the VPN as well which would bypass a public Wi-Fi’s attempt to DNS poison.
I use a VPN anytime I’m not on my home network just because it’s a super easy way for me to force my DNS to my own custom DNS with Adblock listing on the machine that’s running the VPN endpoint.
It’s wireguard, and it connects to a direct IP address. If someone tries to redirect or otherwise man in the middle of the connection wireguard will simply fail to establish a connection. Thanks to the fact that it uses a similar idea to pgp where the client and server already have each other’s public keys and there’s not really an unencrypted initial handshake even the initial talking has a form of encrypted communication thanks to the key pairings.
So like, my vpn is definitely proving security. Whether or not every random ass VPN you can buy is smart enough to force all DNS over the VPN or anything else I guess I can’t say for sure maybe it’s not common and that’s why but it definitely can be used to help automate some security measures when using a public network
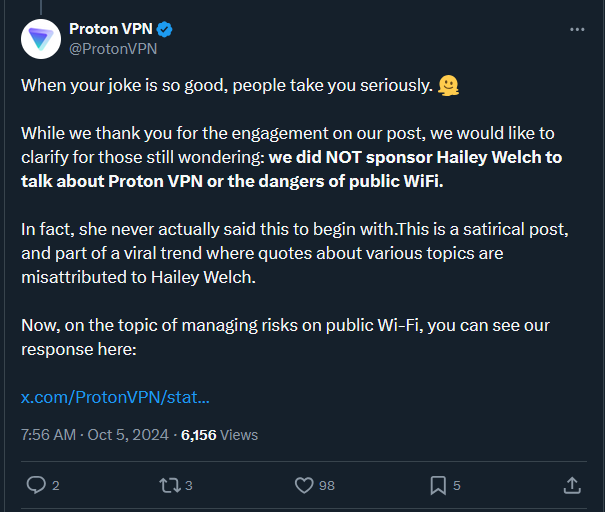
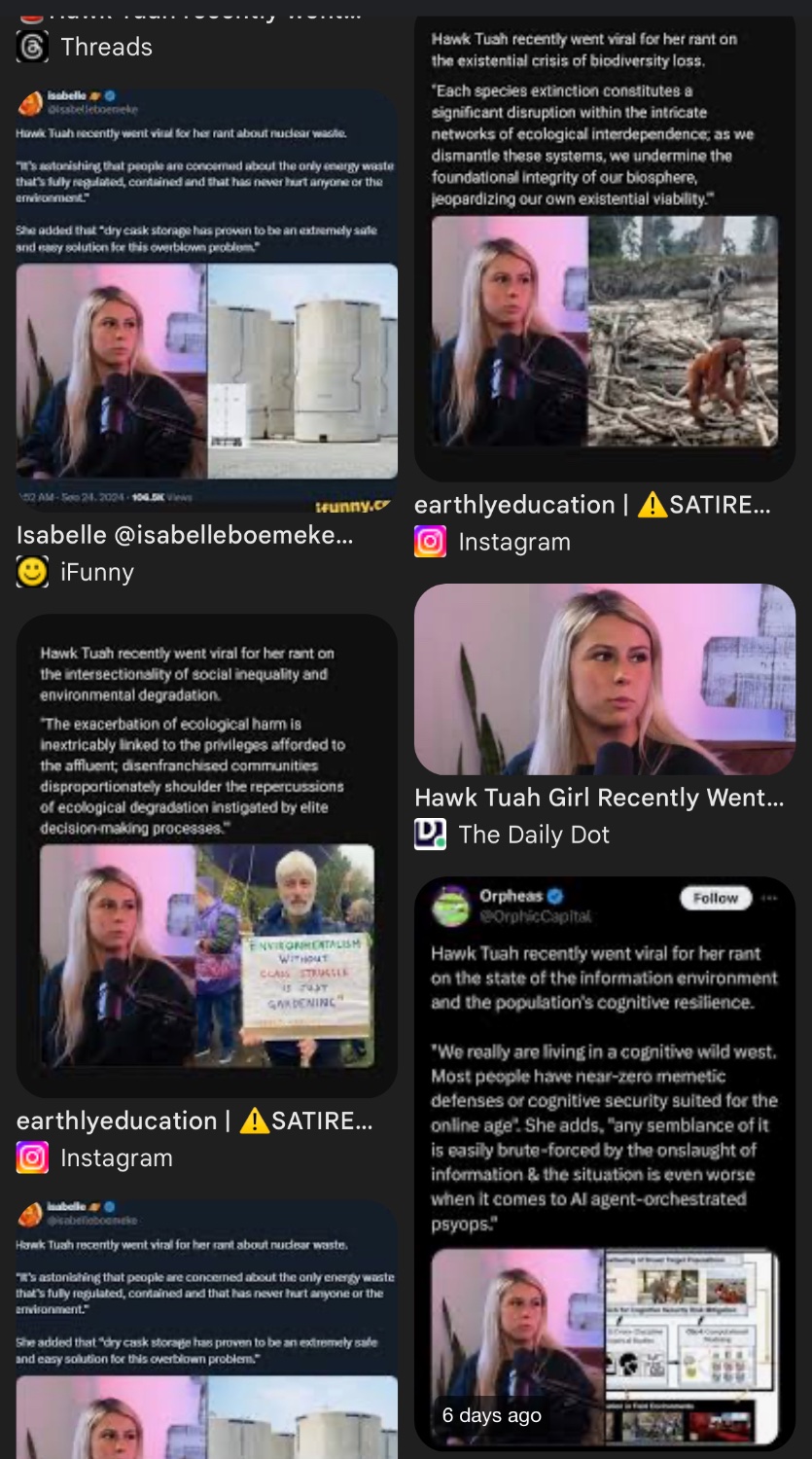
When I first saw this I thought it was funny. The fact that so many people are falling for it has only made it even funnier.
FWIW, Haley Welch might seem dumb as bricks, but she also seems quite sweet - doing charity stuff, keeping her other friend from “that” vid for the ride, etc. As far as people becoming famous for bullshit reasons goes, she seems to be handling it well.
I feel bad for her, honestly. She was open about her sexuality and she’s conventionally attractive, so now she has all these leering old men on TV slobbering all over her.
Bill Maher practically tried to talk her into bed on his show with his creepy shit about mentoring her.
Oof. What is up with these creepy, sweaty dudes on talkshows? I know they somewhat reflect the general populace, but to pull shit like this on air is just boggling.
deleted by creator
You know, you’re the first person I’ve seen that’s shared the same view as me (not that I’ve spoken about the topic much! lol)
Woman admits that she has performed an extremely benign sexual act before - ghasp! A girl has given someone a blowjob before!
And more than that, she has a “dumb” accent! Let’s make endless memes about her online basically calling her a slutty moron whose only life skill is sucking cock.
Honestly no wonder women feel pressured to pretend they have no sexual desires
Honestly, I never understand why people like this get the level of fame that they do, but at least stop creeping on the poor lady.
Okay so I haven’t heard about her before this but, from this thread and a quick google search, I feel like I know enough. Anyway. I’m hopeful then that the fame will pass— lots of internet fad celebrities fade and become more or less normal people again soon— but she pockets enough money to live a good life and keep paying it forward.
I didn’t know who she was, so I just assumed it was true and that she was just another celebrity sponsored by a VPN company.
Yup, I don’t know who she is, nor do I particularly care. What I do care about is how Proton behaves, and if they’re going to stoop to the levels other VPN providers go to in order to attract customers, it’s not a service I’d like to support.
I’m currently not a Proton customer, but I’ve been considering it. I’m currently w/ Tuta for email and use a DIY VPN, but I could see switching to Proton as their product line expands.
Falling for what?
She’s handling fame better than Chappel Roan.
You think she’s not handling fame well because she’s setting clear boundaries, and reminding fans that she’s not their friend just because she’s famous?
No, because she has a reaction video to every single negative thing anyone says on TikTok. I’m all for her boundaries.
she has a reaction video to every single negative thing anyone says on TikTok
Ew.
I don’t know how effective VPNs are over a public WiFi network, but I do know it stopped Spectrum from sending me “you are downloading copyrighted material, stop it” emails once I started using one. Fuck Spectrum, I don’t have them anymore, but that seems like a good enough reason to keep using one in certain circumstances.
They need to advertise a legitimate use for their service.
If they don’t have a threat from public wifi or other security concerns to remedy, then the only purpose for their service is to bypass region limits and block infringement notices. They would be considered complicit in such infringement.
That their service also hinders efforts to stop pirates needs to be an “unintended” and “unavoidable” side effect.
I use Proton when I’m on my university’s campus because they switched to using EDUroam for the campus wifi. I used to be a Sys Admin at a different university a while back, and from what I know, EDUroam allows the IT department to monitor basically all of the traffic over the network. I don’t know exactly how deep that stuff goes, but if I was doing anything personal or sensitive like banking or whatever, I’d flip on the VPN on my personal computer. I also don’t have any personal accounts logged in on the school issued laptop because they have it loaded with institutional spyware. Once I graduate, I’ll blank the drive and reinstall the OS to have a decent Lenovo laptop on hand as a spare.
Edit to add: I use Proton because it was the least shady service that I could get for a reasonable price as a student. It is also helpful for finding textbooks. :)
They can’t decrypt HTTPS unless you installed a certificate controlled by them. The only thing they can know is which domains you visited, but not what you did on it.
They require the certificate to be installed to have access to the network.
There are plenty of legitimate uses for their services, they just aren’t things that the vast majority of people actually need. For example:
- access things in a LAN from a WAN - i.e. access a personal PC when you’re at a friend’s house, and your home LAN is behind CGNAT
- get around local laws - e.g. my state requires ID checks for porn and social media, so getting a VPN one state over gets around that
- prevent ISP from seeing the sites you visit - very valid privacy concern, especially since SNI exists to de-mask TLS packets
There are also some sketchier needs, such as:
- get different content on your streaming platform
- hide sharing of illegal content (i.e. piracy)
- perform illegal transactions (e.g. going on Tor to buy drugs or whatever on the black market)
I think VPNs are trying to appeal to more than just the above needs, they’re trying to create needs to grow their marketshare. That isn’t something a reputable VPN should do, or at least that’s something that would make me hesitate to use a given VPN.
If you want to give an anonymous video to the press or the police. If you don’t hide your ip then it isn’t anonymous and they’ll come question you.
get around local laws
That’s not a legitimate use; it’s an illegal use just like piracy is.
especially since SNI exists to de-mask TLS packets
ECH will finally fix this. https://blog.cloudflare.com/encrypted-client-hello/
SNI is still better than what we used to have. Before SNI, every site that used TLS or SSL had to have a dedicated IP address.
That’s not a legitimate use; it’s an illegal use just like piracy is.
My understanding of the law (and yes, I read it) is that it’s not illegal. The law in my state is for service providers to authenticate the ID of any state resident, it’s not a requirement on the resident themselves. The service provider isn’t aware what state I’m a resident of, and state law doesn’t apply outside the state, so I don’t know what law would be violated here.
SNI is still better than what we used to have.
I absolutely agree, and I actually use SNI to route packets for my homelab. Without SNI, I would have to route after handling certificates, which would be annoying because I want TLS to work within my home network, and I mess w/ DNS records to point to my local IPs when inside my network. I could have everything routed through a central hub (so one dedicated machine that handles all TLS), but that’s a single point of failure, and I’m not too happy about that. Or I guess I’d have multiple IPs, and route based on which IP is being hit.
I’ll have to check out ECH. Hopefully I can eat my cake and have it too.
The only thing you need to say is “my ISP uses CGNAT” you can’t host anything or run games for your friends without a way to punch through the CGNAT layer. I mean you could use IPv6 if it weren’t still a joke in the US but here we are.
Yup, CGNAT sucks. But STUN works fine for me, and most games support it, so it’s not a huge issue.
I could pay extra for a public IP, but for the same price I can get a VPS and do other cool stuff, so I just went the WireGuard VPN route. Same end result with a little more latency, but also more flexibility. I host a few static sites directly on the VPS, with everything else going through the VPN, so that’s nice.
I’m not defending Proton. I don’t even use them.
Edit: The region limits thing is nice though. It’s not why I got the VPN, but it’s nice to not have to pay to watch the Olympics and just watch it via the CBC or the BBC.
On public WiFi I just vpn into my home network. The issue with public WiFi is that it can be sniffed by anyone in range since there is generally no encryption.
Although pretty much everything we do is over tls these days, and DoH helps protect against even dns sniffing. There’s still at least some risk to working in the clear over a public WiFi network. At least in information gathering, what bank you use, etc.
But, there’s no real benefit in using a paid vpn over one you own unless you’re downloading illegal content, want to watch another Netflix region, or are in a country with heavy Internet monitoring/filtering.
With TLS and DoH, how is your bank and other information leaked?
Possibly the domain is visible with a traffic monitoring tool. Everything else is between you and the bank via HTTPS. Having said that, whatever is not over https is visible to whoever sits on the same network as yourself.
Importantly, you probably don’t know what all is encrypted in every app you use on your phone, so it’s best practice to encrypt the transport.
I experienced the same with Cox Internet.
All ISPs are legally obligated to forward that shit to you. The alerts are not from spectrum, they’re just relaying the information.
Right now, copyright owners do not have legal permission to find out who you are directly without a court order. They would only seek that information if they were planning to file a lawsuit.
Media companies know, from the Napster incident, that such actions can backfire stupendously. It’s rare that they even bother anymore. I can go into detail on why, but I’ll leave it out for brevity.
So they send the notice to your ISP, who is legally obligated to match the information on the notice to the subscriber and forward the notice to you.
For many, this goes to an ISP provided mailbox, which most people ignore the existence of it. Clearly spectrum operates differently.
The notices are from copyright holders who have no idea who you are, and can’t determine that information unless they intend to sue you. So those can be, for the most part, ignored.
It’s not your ISPs fault that you got those. They couldn’t give a shit less about what you do on their service, or what you download. They just want you to pay your bill every month and keep the gravy train rolling.
I’m saying fuck Spectrum for other reasons. Either way, there’s less of a trail.
Fair enough. I haven’t used spectrum, so I have no opinion. I’m not in the right country to subscribe to their service, so there’s that.
Have a good day.
Spectrum is a total shit ISP that does shady shit constantly, while being owned by a massive corporation run by a Trump supporter and unfortunately is the only option people have in a lot of places in the U.S.
Anyway, good talk. You have a good day too!
Considering how most of the Internet is encrypted with TLS, if you add DNSSEC+DoH/DoT on top, trying to MITM someone on a public WiFi is way harder than it was, unless you’re a state-level adversary and you’re able to craft valid certificate for a domain you don’t control from a globally trusted (root) certificate autority (which will lose its trusted status quite fast once discovered, ex: CNNIC)
Not all applications on your computer may be encrypting their packet traffic properly, though. That goes especially for the applications that might be trying to reach out for resources on your local home network (like printers, file shares, and other home servers) as well as DNS requests which are usually still made in the open. I would not recommend eschewing an entire security layer willy-nilly like that. On public Wi-Fi, I would definitely still suggest either a VPN or using your cell phone as a tether or secure hotspot instead if possible.
Sure, but it’s also like, if you’re stepping away from your laptop for a few minutes should you lock the screen or shut it down completely.
The most secure option is to shut it down completely, but also it’s fine to just lock your screen.
If you’ve already got a VPN and it’s as easy as locking your screen to enable, go for it, use it. But if you don’t, you don’t need to go out and get one. You’ll generally be ok without one.
The most secure option is bringing the laptop with you.
I mean, technically - the most secure option is irrevocably destroying the laptop everytime you have a break.
The most secure & economical option is to never go outside
As a network security expert, I’ve got that on LOCK
Oh so a one time pad
Yeah, the days of your local coffee shops Wi-Fi being a problem or mostly gone. Not the VPN doesn’t have a place anymore though. If you’re trying to hide your downloading of ISOs from your ISP it’s still a perfectly reasonable method. Or temporarily relocating yourself to another country to make a purchase or watch some streaming content both perfectly reasonable.
Of course some of the streaming providers are getting wise to this.
why would I need to hide my terabytes of Linux ISO downloads?
Bill Gates, man, Bill Gates
It’s all fun and games until a Microsoft Purity Enforcement squad is kicking in your door.
Nah, it’s all good I subscribe to Linus Torvalds protection services. When the Microsoft vans get within four blocks of my address, They’ll drop ship in dozens of fully-armed penguin paratroopers. After the incursion they even send in a penguin based cleaner team to help get rid of the remains.
You don’t want their admin to contact you about how you’re a n00b for not using Arch.
Because we see which distros you’re using, and we judge you for it.
Gentoo, in 2024? Really? You should be using Arch if that’s your thing. It’s not the 90s any more.
Arch? I prefer EndeavorOS as it lets me easily install an arch distro using a nice GUi, I really don’t care about the nitty gritty of setting up my own network manually, i am like 99.9% of people in that regard
I have a VPN so I can securely access my home network when I’m away
Yeah, pptp will always have a strong purpose and home. I’m more speaking to the viability of commercial anonymization VPN.
I have a feeling you are using pptp as shorthand for Point to Point disregarding protocol and already knows what I’m about to say. To anyone else reading this - PPTP is obsolete and unsafe. Use an alternative such as OpenVPN, WireGuard or SSTP.
Tailscale FTW. I honestly haven’t looked at the underlying protocols in years. Was using ubiquiti’s implementation of openVPN but it seemed to get grumpy when you connect one user multiple times.
Poking around at available products, I had settled on zero tier and tailscale, I went ahead and tried tail scalefirst because it was basically free for my house. One month in, I had a few decent detectable guys at work join me on a trial there. Full licenses for everybody at work cost less than my Cisco refresh. And makes it so that the office is no longer a critical hosting site.
OpenVPN allows multiple connections if you enable duplicate-cn:
–duplicate-cn
Allow multiple clients with the same common name to concurrently connect.
In the absence of this option, OpenVPN will disconnect a client instance upon connection of a new client having the same common name.
https://openvpn.net/community-resources/reference-manual-for-openvpn-2-4/There’s also headscale if you wanna selfhost the tailscale control server:
https://github.com/juanfont/headscaleIt was allowing me to make multiple connections but they were unpredictable, I assumed it was a unifi problem back in the day thanks for the information!
I use a VPN for the same reason I use the Internet. Porn.
That’s not what these commercial VPNs are for.
Or the tld is .mobi
Interesting read, thanks!
I’m not online enough to understand this.
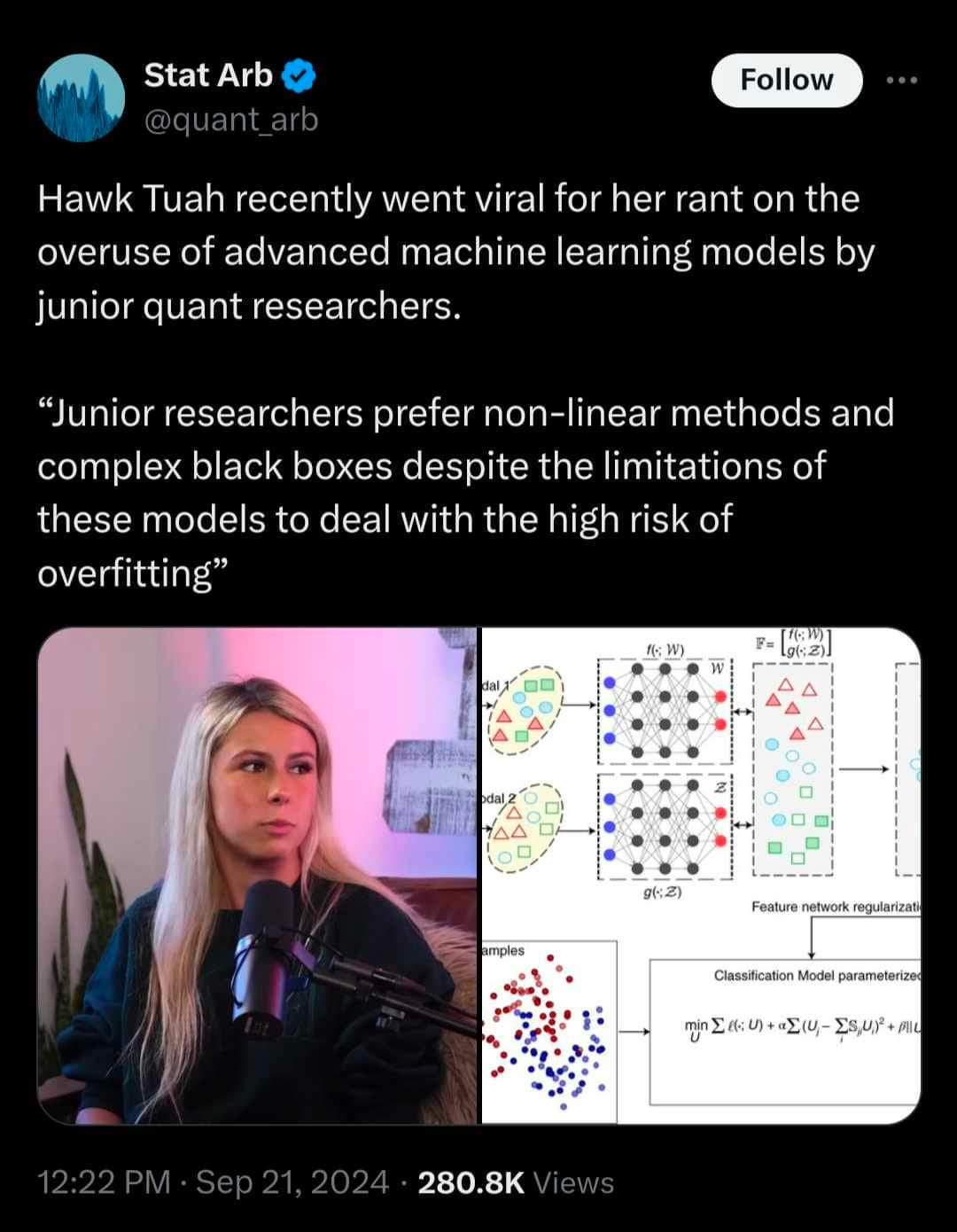
Hailey “Hawk Tuah” Welch is an influencer that gained a lot of popularity from her nickname (the sound of spitting, with HEAVY implications of performing fellacio). She used her platform to voice a very reasonable and intelligent opinion, which surprised a lot of people because her nickname is essentially blowjob queen.
One of her opinions is that it’s important to spread cyber security and used her fame to try to educate the public (potentially a fake story from the image? Idk this drama). And some xit-head claiming to be a cyber security expert ate the onion and offered some shitty advice. Proton fact checked them, because there are a ton of fake news stories about her right now.
I’m pretty sure that Proton quoting her in the first place is fake. I know she’s milking her 15 minutes of fame for all she can, but this seems outside her experience.
but this seems outside her experience.
When has that ever stopped people from saying shit.
Sorry, not just implication; she was straight up talking about that.
deleted by creator
Popular format
Thanks for clarifying. This thread has felt like the cyber security equivalent of the Flat Earth Theory.
Hailey “Hawk Tuah” Welch is an influencer
Ah, OK, I’m out.
deleted by creator
Throw a brick at it.
that’s gonna brick it. it’s right there in its name.
people on the internet and their advice sometimes, ffs.
Nah, you just gotta do it correctly, yeah you might brick a few computers, TVs, cars or a couple electrical mains boxes, but once you master the technique you’ll be able to restart anything.
We call that percussive maintenance… the brick is optional.
That’s just turning it off with Style✨
I don’t understand why everyone assumes using a VPN means paying for a third party. I have Wireguard deployed in my NAS and I always have that VPN connection active on my phone to be able to access my LAN deployed services remotely, Jellyfin for example.
Most VPNs sell themselves on encrypting your traffic to an endpoint that either is in a different locale to get around region locks or to put it out of the grasp of the RIAA so they can’t send your ISP copyright notices.
While remote access to a local network is a good use case for a self-hosted VPN it’s totally unrelated to the use case for commercial VPNs
For the use case of encrypting your traffic while using a public WiFi, both commercial VPNs and self-hosted ones provide the same functionality.
deleted by creator
Yes, but this thread is about security while using public Wi-Fi, which the original comment was saying doesn’t require commercial VPNs.
And I highly doubt people are pirating while on public wi-fi, the bandwidth just isn’t good enough, and even if it was, it would be a dick move to other public wi-fi users.
Yes that’s true. But also that’s the wink and nudge marketing claim that VPN marketers make while everyone knows the real reason you are using a VPN.
With HTTPS, DNS-over-HTTPS, and most endpoint firewalls dropping non-gateway traffic, the risk is a lot less than the VPN ad reads want you to believe
DNS-over-HTTPS sounds like it’ll be the least used by general public since most people I know are still using default DNS settings which would point towards their ISP’s. I’m not sure how many ISPs have moved towards DNS-over-HTTPS or if they are even activated by default.
Firefox has DoT enabled by default, maybe Chrome does the same. That would cover the use-case of most people on public wifi.
Wait, it’s set in the browser? I’ve always thought you set that at the OS level.
Both, the browsers (and any other application) can choose to ignore your DNS settings and use whatever other mechanisms they like.
deleted by creator
Since Wireguard uses UDP and peers only reply to a received packet if it’s expected and valid, it won’t show up in port scans and barely increases your attack surface. Tailscale and Zerotier are quite nice, but personally I dislike NAT-punching protocols.
I use tailscale for hosting gameservers for friends and the occasional watch together on jellyfin. Kinda scuffed setup with one burner github account for login. And ~10 devices connected to that network. So I need to authenticate every device myself (at the beginning and sporadically) but I don’t need to pay Tailscale for adding multiple accounts to the network.
At the beginning I tried to do set up everything with my own wireguard server. I only have a public v6 IP, so some of my friends connected without problems and for some it would not work. After I think 3h helping them in their router settings I just gave up. I looked up if I could rent a service somewhere that gives me a public Ipv4 relay, found Tailscale instead and stopped looking for something else haha. Sometimes it’s not worth the effort.
Tailscale w/burner GitHub for watch together
Oooooooh
Noted 😎
I am technical, I decided to just not open up any port that’s not needed for Plex and Jellyfin, sometimes it would be nice to access radarr and sonarr remotely, but fuck I just don’t want to deal with the setup
It’s also worth mentioning that the VPN in question, Proton, offers one of the best free tiers of any VPN company.
Agreed. I’ve used it, and it’s perfectly fine for normal web browsing. In fact, I added it to my router a while ago to test it out, and I’m considering leaving it on as a “secure” SSID so we can use it for things that my state requires ID for (e.g. porn and social media).
I don’t understand why everyone assumes using a VPN means paying for a third party.
It’s because that is what is advertised to them.
My setup as well (plus encrypted DNS for good measure)
I still have to somehow trust my ISP but I go down from having to trust my mobile ISP, my employer WiFi, random shops WiFi to just one ISP (that,fwiw, has shown to be transparent, customers friendly etc)
I tried setting this up, and I can connect to my honeserver, but I’ve no idea how to access its LAN services. How does it work?
Do you have internal DNS set up? I have my wire guard deployed on both of my pihole servers, which have local DNS entries for my internal services, which point back to my internal Traefik container for NAT translations. I know that sounds a bit complicated, but that’s how it works for my environment.
Wow yeah, that’s way more than what I have haha. So I guess I need to look into DNS…
Yup, I have the same, but not to access services on my devices, but to tunnel services so they can become public services. Basically, Jellyfin is accessible at mydomain.com, which tunnels traffic over WireGuard to my internal Jellyfin instance. I’ll connect to the VPN occasionally if I need to access something else on my network though.
That said, I’ve considered paying for a VPN service so I can get around my state’s stupid ID laws around porn and social media, which I consider to be a massive privacy violation. But it hasn’t bothered me enough to actually spend the $5/month or whatever.
I do the same, but it’s very clear that when people talk about “a VPN” they’re referring to a commercial cloud hosted product.
IMO, the post is centered around proton VPN, and since that’s a public VPN service, it’s the focus of the discussion.
Private VPNs are a very different story.
This was nothing more than a poorly executed joke from Proton. Some people are massively overreacting.
How could one have known that this was meant as a joke?
I like Proton but to me it seems like the social media person from Proton did an oopsie and as a reaction they try to save it.
The joke is a popular meme of making up things that are happening on the podcast that obviously do not fit the general idea of the podcast. If you are aware of these memes, you’d probably understand the joke right away.
I still think it’s not a good joke to make since it can be easily misleading. I’m not sure there was a good way to make this joke while clarifying it was a joke, and they would’ve been better off finding some other meme to make a joke with.
I think the biggest problem with the joke is that Proton somehow didn’t understand their audience at all. I would imagine it leans older and most of their followers wouldn’t get it. Most of my Gen Z friends would have understood the meme, but I doubt many of them follow Proton on Twitter.
As always.
obviously the shitty VPNs like NordSurshark, TorGuard, Tunnelbear, cyberghost and PrivateInternetExpress suck…pretty much every VPN that’s part of some giant conglomerate sucks ass in terms of privacy and security
But then there’s iVPN, Mullvad and ProtonVPN and even Adguard VPN which do very little to no advertising at all and allow their products to speak for themselves. I mean…Kitboga and RionaPoison are sponsored by Proton, but Proton is a good company that takes their security and the security of their swiss-law-abiding users very seriously.
Don’t be a scumbag and Proton won’t snitch on you.
The VPNs you characterise as “shitty” aren’t necessarily a bad choice; they’re cheaper than the legitimate privacy VPNs. Mullvad is famously 5€ per month, Proton is 4.49€ per month, but NordVPN is 3.09€, Surfshark is 2.19€, and PIA is 1.79€ per month.
If you’re really just here to pretend you’re in another country (rather than privatemaxing) or hide your torrenting activity from your ISP, the cheaper options can be a perfectly legitimate choice.
Mullvad doesn’t try and lock you in with any auto-renewal shenanigans and was the second service that I know of to offer payment via xmr. The first was ivpn but their server speeds were trash.
That’s true. Mullvad will even let you send cash by post to them which is definitely not something you can do with other services.
However, in terms of private payment options, you can always use BTC’s Lightning Network with the other options if that concerns you.
I believe Proton VPN allows for cash mail in. https://protonvpn.com/support/payment-options/
It seems you’re right. I did not know that.
they do. They also accept bitcoin
Love it. If you want to stay anonymous, might as well go the whole way. Granted TOR should not be used with a VPN.
The first was ivpn but their server speeds were trash.
Their server speeds are great now. I tried them. They just have a very small number of servers compared to those other three
https://thatoneprivacysite.xyz/ is a good base for comparisons
Bear in mind that info hasn’t been updated since 2019, when the OG thatoneprivacysite sold out to a shady company. The .xyz site is an old backup someone put up of the site before it changed to only recommend a handful of bad VPNs.
Is there a more recent guide that you’d recommend?
Perhaps Privacyguides.org, but I’m not aware of a replacement for the exhausting level of detail and breadth which thatoneprivacysite once provided.
Just what I was looking for. Thanks.
I have a vpn for… reasons… 🏴☠️⚓️🏴☠️
I have VPN so I can look at porn.
I just wanna look at me Japanese cartoons
Dude!
deleted by creator
I assumed it was a joke. My feed has been full of jokes about her talking about urban planning and transit oriented development.
deleted by creator
I’m sure as shit trusting proton over some random public network in a cafe setup by some random open reach engineer or something
They have 54% one star reviews on TrustPilot
But none that I saw were about security/privacy instead just comments about pricing.
Thank goodness someone explained that to me. I was startong to wonder if she was some sort of technology expert, or something.
Who is she?
the girl from the memes a few weeks ago https://knowyourmeme.com/memes/hawk-tuah-girl
It’s that recent. Jeez. Feels like it’s been a thing for months.
Wait, what day is it? WHAT YEAR IS IT?
OH GOD
Don’t hire that contractor lol
Can someone share proton’s response? I don’t have a xitter account
https://xcancel.com/ProtonVPN you can find it here
Appreciate the alternative!
Grabbed this screenshot because I don’t trust anything on Twitter to stay visible (or the platform to even be stable)
https://protonvpn.com/blog/public-wifi-safety/#:~:text=5 ways to stay safe on public WiFi

Wow, one of a few heroes keeping Nitter alive
Fr
Nobody has a Xitter account.
Millions and millions of idiots do.
Is this some highly-voted pedantry about the site not technically being called “Xitter”? Or wtf is going on in this thread…?
I thought they were mostly bots and alts
Nobody that matters has a Xitter account*
This was poorly executed. The National Park Service twitter account does jokes well.